On July 2nd of this year, a Russia-based, professional hacking group called REvil hit the managed IT service provider Kaseya with a massive ransomware attack, affecting roughly sixty managed service providers and nearly 1500 businesses worldwide. REvil asked for $70 million in ransom to decrypt the files at first, then later dropped their demand to $50 million.
Blog
Ransomware and What You Can Do to Avoid It

The BBC reported this week that several schools on the Isle of Wight in the British Isles were hit with a string of ransomware attacks. Ransomware is a form of cybersecurity breach in which a cyber criminal either threatens to release private information to the public or block access to their data altogether until they pay some kind of ransom.
An Intro to Cryptocurrency

Quick Announcements:
-Microsoft has released official system requirements for Windows 11, and is teasing an October release date for a free downloadable OS upgrade for existing users. Check out our write up on Windows 11 here.
-Shortly after President Joe Biden signed his recent executive order, the FTC voted unanimously to uphold right to repair-style regulations across the country.
Right to Repair

Earlier this month President Joe Biden issued an executive order that by his own estimation would stimulate economic competition and roll back monopolistic practices on the part of large corporations. One part of the order includes measures relating to tech companies preventing consumers from either personally repairing broken proprietary hardware, such as a smart device or an electric car, or hiring a third-party repair company to do it for them.
The Future of Cybersecurity

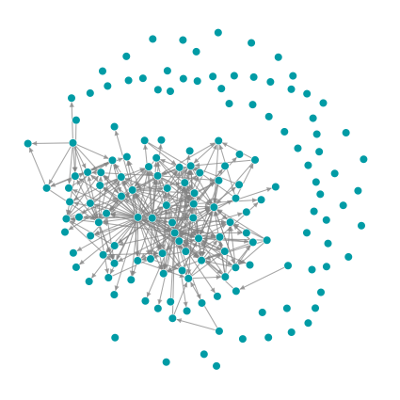
There are numerous cybersecurity risks that any enterprise leader needs to consider when planning out their organization's IT infrastructure. Security breaches can come from something as simple as a bad password, or--even worse--a bad password that's repeatedly used for multiple accounts within the firm.
A Crash Course in 5G
Microsoft Announces Its New Operating System

Microsoft presented a preliminary version of its new operating system, Windows 11, last week in a roughly forty-five minute long video announcement. This is the first official confirmation of a new operating system from Microsoft since the release of its previous operating system, Windows 10, in 2015. Windows is arguably the most widely employed operating system for both personal and business use.
Update Errors, Crashes, and You
Social media platforms, such as Reddit and Twitter, are abuzz this week with news of a recent update for the Google app on Android phones , which has led to widespread crashes and error messages, preventing users from utilizing the app. The severity of the problem seems to vary between phone manufacturers, with some phones receiving error messages that effectively make the app useless while others aren’t affected at all.
Clear And Unbiased Facts About AI-Driven Cyber Threats
There have always been security risks for businesses, now it's just migrated across the physical realm to cyberspace. And today's global world revolves around "information," which relates directly to both companies and customers. Because business operations have become sharper with innovation, so have cyber attacks.
Ransomware Threats: What SMBs Need to Know

Imagine this: You've worked endlessly over the past month to make a video collage of your parents' treasured memories together for their golden anniversary. You've included the correct pictures, overlaid it with music to make nostalgic recollections of their favorite songs and imparted flawlessness.